dappy

A global internet naming technology for high value web services.
Dappy is a new internet domain naming technology, developed since 2021, and live since 2022. We developed from scratch a domain name system (scoped with .d) that is developer friendly, designed for web services that need maximum security, operated in a collective fashion by a network of professional companies and foundations.
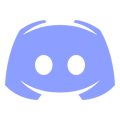
The issues with the current system
Today each company in the DNS secures its own address space (.com, .net etc.), there are single points of failures everywhere. SaaS, B2B companies, even the one deploying multi-Billion web services must choose and trust one domain registrar, one domain registry, clients trust one DNS resolver and also every single certificate authority for HTTPS certificates distribution.
Understanding dappy in two steps 🙂
Dappy proposes a radically new approach for both storage (DNS and TLS data) and service discovery. It is a new protocol that operates independently of DNS and the Certificate Authorities system.
(1) Multiple companies and foundations secure and own the same address space (.d), the larger the network is the stronger security and privacy is for service discovery.
In DNS, each company secures its own address space. Additionally hundreds of HTTPS authorities must be trusted.
In dappy, multiple companies secure the same address space together through a permissioned DLT.
.d
FABCO
Pathrock

Open slot
Open slot
Open slot
Open slot
(2) Clients (web browsers, operating systems, runtimes) do service discovery with co-resolution. They ask many nodes instead of one for the IP addresses and TLS certificates (and other data that may be stored on dappy).
Adoption and browser compatibility
Dappy can be used for APIs and SDKs at the moment, but not for web applications as major browsers don't do co-resolution, and don't resolve .d domains. We welcome private companies and foundations, as well as public government agencies to strengthen the network, and benefit from the revenues (each company gets the same income from domain names).
Events
March, 2022
FIC - cybersecurity
 Lille (France)
Lille (France)
April, 2022
Vivatech
 Paris (France)
Paris (France)
November, 2022
Web Summit
 Lisbonne (Portugal)
Lisbonne (Portugal)
January, 2023
CES
 Las Vegas (USA)
Las Vegas (USA)
October, 2023
GITEX
 Dubai (UAE)
Dubai (UAE)